This weeks’ hands on activity really helped me better understand how much of modern technology depends on secure, well-managed access systems. We focused on Identity and Access Management (IAM) and Multi-Factor Authentication (MFA), and I found myself reflecting on how these concepts connect to my own experience working at IDT.
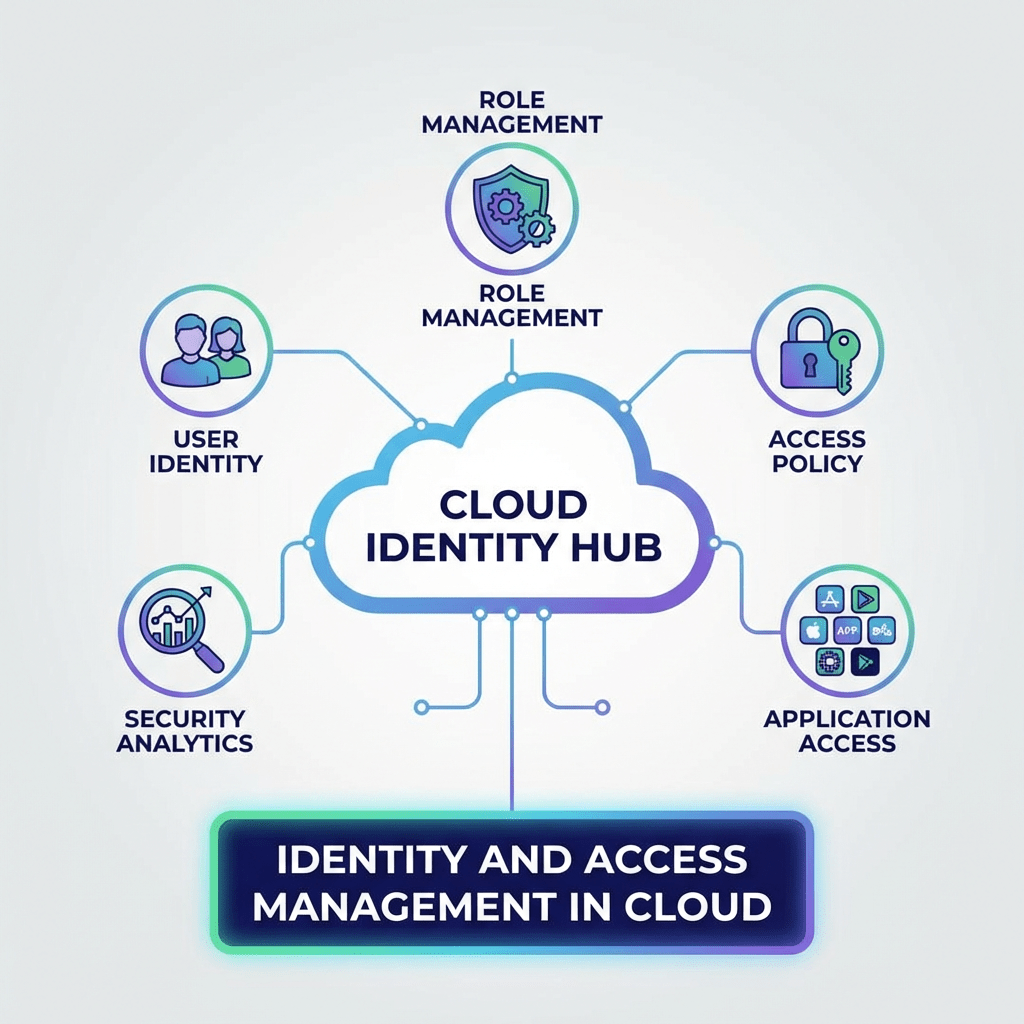
At its core, IAM is about making sure the right people have access to the right resources at the right time, and nothing more. That sounds simple, but when you think about the amount of sensitive data companies handle, it becomes clear how critical this is. In a company like IDT, where systems, internal tools, and potentially sensitive information are involved, IAM acts as a gatekeeper. It determines who can access what, whether it’s internal platforms, communication tools, or data systems. I faced this often when trying to build a machine learning tool that would automate our DNA collection. Much of the data required special permissions.
One of the biggest takeaways for me was the importance of Multi-Factor Authentication (MFA). Before learning more about it, I understood it as just an extra step during login, but now I see it as a powerful layer of defense. Even if a password is compromised, MFA can stop unauthorized access in its tracks. Thinking back to my time at IDT, this makes me more aware of how important those extra verification steps really are. They’re not just an inconvenience; they’re actively protecting both the company and the individuals within it.
We also talked about the risks of not having a strong IAM system, and that really stood out to me. Without proper access controls, people might have more permissions than they need, which can lead to accidental mistakes or even intentional misuse. In a fast-paced work environment like IDT, where there are multiple people interacting with systems throughout the day, it would be easy for things to go wrong if access isn’t carefully managed. Another key point was what happens when someone leaves a company, if their access isn’t removed immediately, that creates a serious vulnerability.
Comparing cloud systems to traditional on-premises systems also gave me a new perspective. Cloud computing allows for more flexibility and accessibility, but it also means that security has to be tighter and more intentional. IAM becomes the main line of defense, rather than just one part of a larger system. This made me realize how much trust is placed in these systems to function correctly and securely, especially when access can happen from virtually anywhere.
Overall, today’s lesson made cloud computing feel much more real and relevant to my own experiences. It’s not just abstract technology, it directly impacts how companies operate, protect their data, and maintain trust. Reflecting on IAM and MFA in the context of IDT helped me see how these concepts are already part of my world, even if I didn’t fully recognize them before. It also made me more aware of my own role in maintaining security, even in small actions like protecting login credentials or following proper access protocols.
This is definitely something I’ll be thinking more about moving forward, especially as I continue learning about technology and its role in both research and industry spaces.

Leave a comment